How Pistachio Handles Recovery
How Pistachio Handles Recovery

How Pistachio Handles Recovery
How Pistachio Handles Recovery

Account recovery is a critical part of any self custodial wallet. Users need confidence that if a device is lost or replaced, access to funds can be safely restored. Pistachio is designed with a recovery system that prioritizes clarity, security, and user control.
Your Signing Key Stays on Your Device
Pistachio uses a model where the full signing key exists only on the user’s device. It is never transmitted, never stored on Pistachio servers, and never accessible to third parties. All transaction signing is performed locally.
This guarantees that only the user can move funds. Pistachio cannot sign transactions or reconstruct keys under any circumstance.
How Backup and Recovery Shares Work
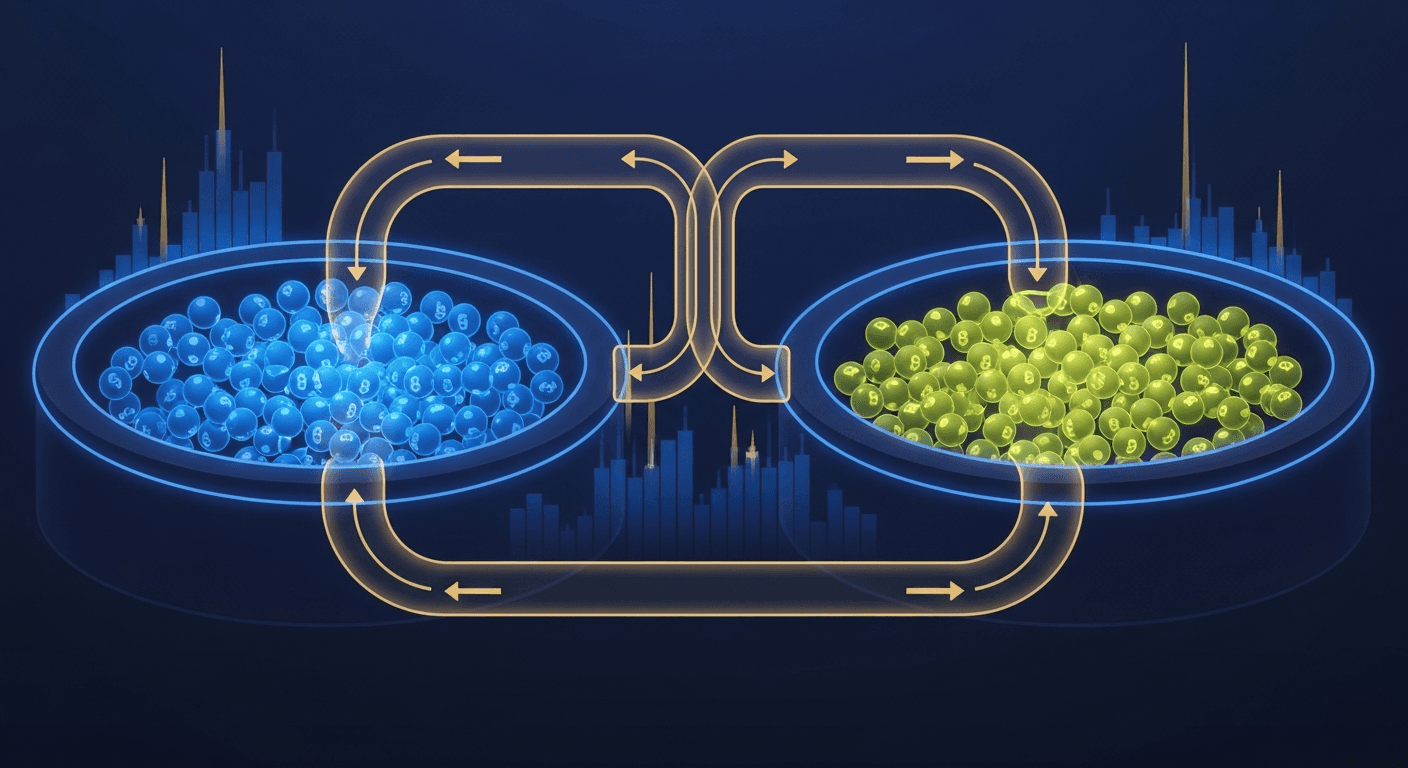
To enable secure recovery without introducing seed phrases, Pistachio creates two encrypted recovery shares when an account is set up.
One encrypted share is backed up to the user’s cloud account.
The second encrypted share is stored on Pistachio’s secure servers.
Neither share contains a complete or usable key. Each share represents only a portion of the recovery data and cannot be used independently.
Even more importantly, these two shares cannot be combined into a signing key without the user explicitly initiating recovery and passing authentication checks.
User Authentication Is Required for Recovery
Recovery can only occur when the user performs a verified action to restore their wallet. The process requires:
Logging into Pistachio on a new device.
Passing a liveliness check through both a one time password and biometric verification.
Authorizing the recovery operation.
Only after these steps does Pistachio allow the device to retrieve the two shares and begin the recovery process.
Even if the cloud share and server share were somehow accessed in their raw form, they cannot be combined or decrypted without the user’s authentication and explicit consent.
This ensures that recovery is always user driven, not system driven.
Local Key Reconstruction
Once the user has authenticated:
The new device retrieves the encrypted cloud share.
The device retrieves the encrypted server share.
Both shares are decrypted locally using the user’s credentials.
The device reconstructs the full signing key.
The complete key exists only on the user's device after this process. Pistachio never sees it, cannot recreate it, and cannot access it.
Security Benefits
This system creates several important trust and safety advantages.
The user retains complete control over the wallet.
Pistachio cannot move funds or reconstruct keys.
Recovery requires explicit user action, biometric confirmation, and OTP verification.
Backup shares are useless on their own, even if unencrypted.
No seed phrases are required.
The result is a modern, reliable, and user friendly approach to self custody.
A Recovery Experience Designed for Real People
Pistachio removes the fragility and stress that come with traditional seed phrase wallets. The system is simple to use, resilient against loss, and grounded in strong security principles.
Your key stays on your device.
Your recovery stays in your control.
Your funds stay protected.
Account recovery is a critical part of any self custodial wallet. Users need confidence that if a device is lost or replaced, access to funds can be safely restored. Pistachio is designed with a recovery system that prioritizes clarity, security, and user control.
Your Signing Key Stays on Your Device
Pistachio uses a model where the full signing key exists only on the user’s device. It is never transmitted, never stored on Pistachio servers, and never accessible to third parties. All transaction signing is performed locally.
This guarantees that only the user can move funds. Pistachio cannot sign transactions or reconstruct keys under any circumstance.
How Backup and Recovery Shares Work
To enable secure recovery without introducing seed phrases, Pistachio creates two encrypted recovery shares when an account is set up.
One encrypted share is backed up to the user’s cloud account.
The second encrypted share is stored on Pistachio’s secure servers.
Neither share contains a complete or usable key. Each share represents only a portion of the recovery data and cannot be used independently.
Even more importantly, these two shares cannot be combined into a signing key without the user explicitly initiating recovery and passing authentication checks.
User Authentication Is Required for Recovery
Recovery can only occur when the user performs a verified action to restore their wallet. The process requires:
Logging into Pistachio on a new device.
Passing a liveliness check through both a one time password and biometric verification.
Authorizing the recovery operation.
Only after these steps does Pistachio allow the device to retrieve the two shares and begin the recovery process.
Even if the cloud share and server share were somehow accessed in their raw form, they cannot be combined or decrypted without the user’s authentication and explicit consent.
This ensures that recovery is always user driven, not system driven.
Local Key Reconstruction
Once the user has authenticated:
The new device retrieves the encrypted cloud share.
The device retrieves the encrypted server share.
Both shares are decrypted locally using the user’s credentials.
The device reconstructs the full signing key.
The complete key exists only on the user's device after this process. Pistachio never sees it, cannot recreate it, and cannot access it.
Security Benefits
This system creates several important trust and safety advantages.
The user retains complete control over the wallet.
Pistachio cannot move funds or reconstruct keys.
Recovery requires explicit user action, biometric confirmation, and OTP verification.
Backup shares are useless on their own, even if unencrypted.
No seed phrases are required.
The result is a modern, reliable, and user friendly approach to self custody.
A Recovery Experience Designed for Real People
Pistachio removes the fragility and stress that come with traditional seed phrase wallets. The system is simple to use, resilient against loss, and grounded in strong security principles.
Your key stays on your device.
Your recovery stays in your control.
Your funds stay protected.

Cross-chain crypto swaps: how Li.Fi powers Pistachio's one-tap zaps (2026)
Etherfuse stablebonds: earn government bond yields on-chain (2026)
How to earn money online in 2026 (crypto yield vs. the rest)

Linea crypto explained: what it is and how it works (2026)

Ethereum wallet guide 2026 (ethernet wallet explained)

DeFi Staking with Stader Labs: How ETHx Works in 2026

High-liquidity crypto exchanges: PancakeSwap guide 2026
What is Raydium? How Solana's AMM Works in 2026

Passive Income Ideas for 2026: 10 Ways That Actually Work
Hong Kong crypto news 2026: licenses, stablecoins, and regulation
©2026 Copyright, PistachioFi Inc.
©2026 Copyright, PistachioFi Inc.
©2026 Copyright, PistachioFi Inc.